April 20, 2026
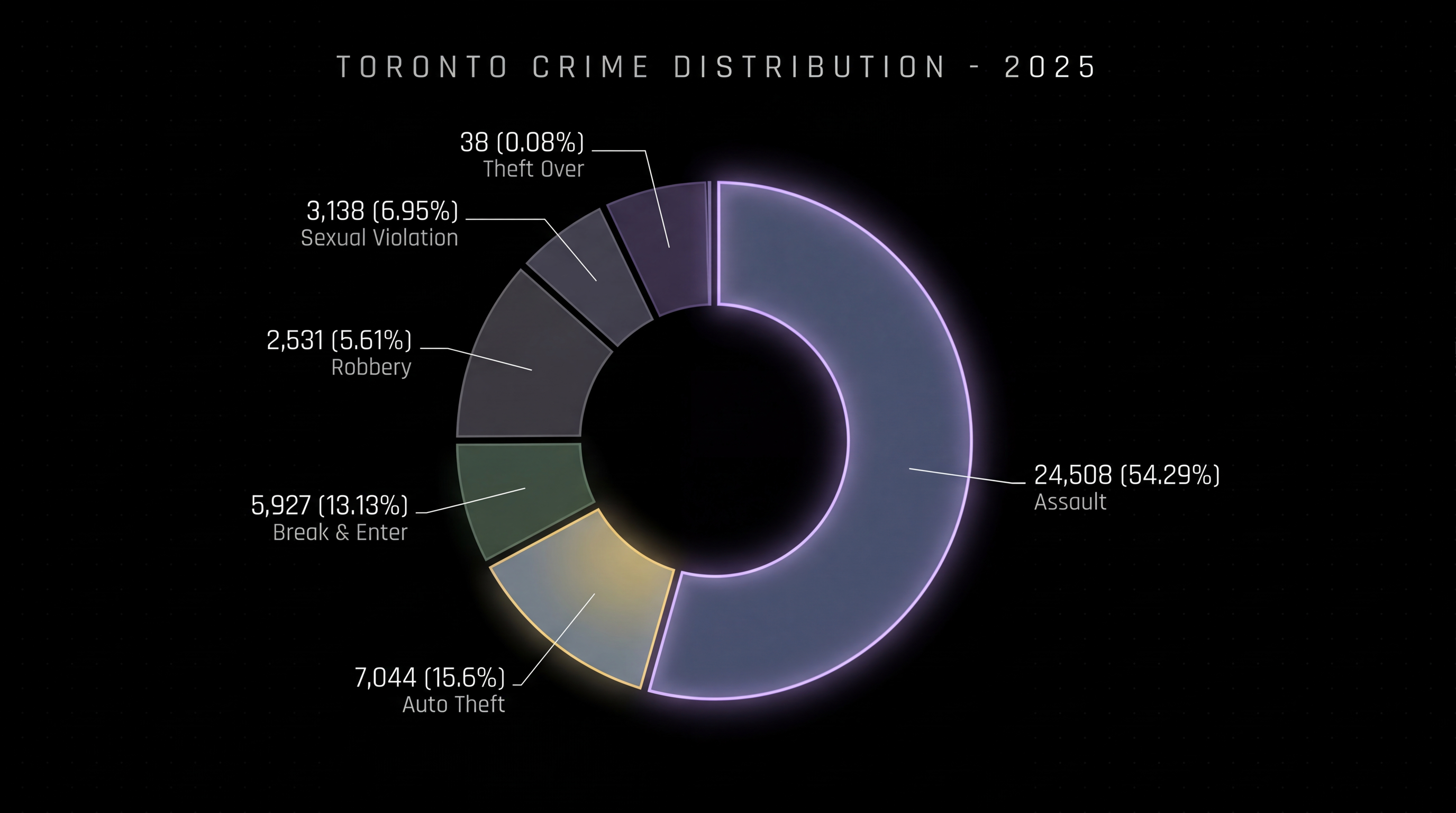
Toronto closed 2025 with some of its most encouraging public safety numbers in decades. Homicides fell nearly 47% to a 40-year low. Shootings were down 43%. Robberies declined by close to 20%. By most headline measures, the city had its safest year in a generation. And yet, one category moved in the opposite direction: theft over $5,000 - the only major crime indicator to increase year-over-year, rising 8.4% and continuing a steady upward climb that has persisted since 2021. That trend line deserves attention.
Read More
March 12, 2026


March 12, 2026

October 28, 2025

January 9, 2026

November 17, 2025
An in-depth look at ambush risk, route planning, evasive driving, and armored vs non-armored decisions in urban environments like Toronto.
Read More
November 17, 2025
An in-depth exploration of how artificial intelligence and human expertise complement each other in modern security operations, highlighting the irreplaceable value of trained operators alongside cutting-edge technology.
Read More
November 17, 2025
An eye-opening analysis of the most common yet overlooked security vulnerabilities in luxury homes, from over-reliance on alarms to predictable routines and untrained security personnel.
Read More
November 17, 2025
Understanding escalation paths, response layers, and why monitoring without action is mere security theater - and how real protection requires intervention capability.
Read More
November 17, 2025
Focus on discreet security, behavioral spotting, layered access control, and intelligence-led planning that protects high-profile events while maintaining atmosphere and guest experience.
Read More
November 17, 2025
Discover how intelligence cycles, threat assessment methodologies, and intelligence-led security strategies once reserved for military operations now protect families, executives, and corporations in the civilian sector.
Read More
November 17, 2025
How live feeds, alerts, AI flagging, and human oversight work together to create an unbreakable security shield
Read More
November 17, 2025
Explore continuous drills, red-team exercises, stress inoculation training, and why operational experience alone is never enough for maintaining elite-level security capabilities.
Read More
November 17, 2025
An exploration of how operational military experience translates into calmer judgment, faster decision-making, and more disciplined security operations in civilian environments.
Read More
November 17, 2025
A critical examination of AI-powered security systems in the Greater Toronto Area, analyzing where artificial intelligence delivers measurable value and where it fails without human oversight, proper data, and operational discipline.
Read More